09 - The key to crypto ownership
“Self-sovereignty” describes the idea that each person has the natural right to exclusively control their own body, possessions, and life. The concept of self-sovereignty was unique to the United States at the time of its founding and played a large role in influencing the type of government that was eventually created.
The system that the founders landed on is a democratic republic which allows citizens to protect themselves and their self-sovereignty through an election process. At that time, the concepts of self-sovereignty and democracy were absurd. A great example of how the idea of democracy was probably received back then is the season finale of Game of Thrones. The very idea of self government was laughable.
After the United States had won the right to attempt this crazy idea of democracy, politics in the country was quickly dominated by two parties: the Washington-Federalist and the Jeffersonian-Republicans. The core belief of the Federalist party was the need for a large national government that had expansive powers over the states and individuals. The Republicans, on the other hand, believed in a powerful local government and expansive individual rights. The early political debates and, frankly, every political debate ever since, are truly about where to draw the line as to where self-sovereignty ends and government rights begin.
What you will find entering the digital asset space is that the individuals in this space have a strong belief in individual rights. An individual has a right to life, liberty, and the pursuit of happiness–AND what they do with their money. A blockchain was designed to allow anyone anywhere to do anything at any time with the wealth they have created. Last week we learned the tool by which the industry enables this– Wallets and the private/public key system enable anyone to simply download wallet software and connect to a blockchain. Users have many options as to what wallet software they want to use, so let’s further break down how wallets work, review your options, and discuss the pros and cons.
How are keys used?
A quick refresher: wallets are key chains. They organize and store your secret phrase and private key, and track your public key. Seed phrases and private keys must be kept secret. They are like the password to a combination lock,--once they are known, the digital assets linked to that wallet will forever be accessible. The relationship between private key and wallet address is foundational to the blockchain space.
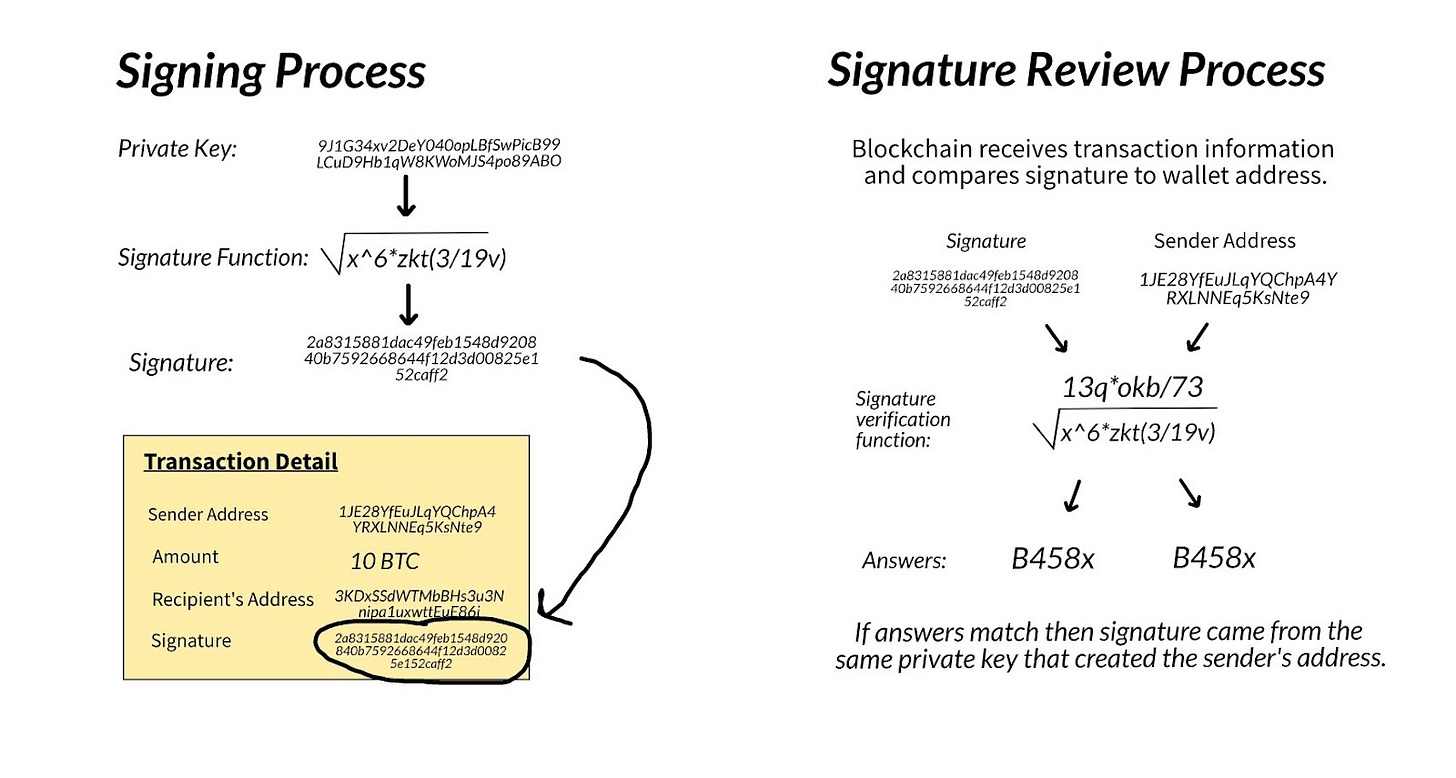
In my earlier post, How the Island of Yap Works Today, we learned that signatures are the way blockchains solved the problem of authenticating transactions. Signatures are a unique identifier that tell the blockchain network that a transaction is legitimate. If you want to send digital assets, you must send the transaction details to the blockchain network. Included in that transaction detail is the wallet address, the recipient's wallet address, the amount, and a signature. Similar to the way in which banks review the signatures on a check, blockchains review transaction signatures. The signature on a check is created using a pen while blockchain signatures are created using a private key.
We learned last week that private keys use crazy math to first create a public key, and then that public key creates a wallet address. When a transaction is sent to the blockchain network, the network compares the signature to the wallet. Remember the private key is indirectly linked to the wallet address through the public key and so is the signature. The math being used allows anyone to tie the signature on the transaction to the wallet address sending it. Thus any user can sign a transaction using a private key, keep the private key a secret, but still allow the network to know that the transaction being sent was in fact created by the owner of that address.
We keep discussing this term “crazy math.” The math equations used are cryptographic functions. You do not need to understand cryptography to understand how a blockchain works, and the model I outlined above is not technically accurate but is conceptually valid. A lengthy discussion around cryptography is something we can discuss another time; but if you are interested, you should check out a more in-depth explanation here. For the sake of this conversation we are just going to use the term “math” and discuss the purpose the math serves in our blockchain system.
First, the math protects the input which in this case is your private key. When we use a private key to create a public key, the math equation is designed in such a way that even if you know the equation and the answer (the public key), you are not able to identify the initial input used (the private key). In this way, I am about to get a result that does not compromise my private key.
Second, if the same initial input is used (your private key) but you change the math, you can tie two answers together. You can connect a signature to a wallet address, meaning that I can send a transaction to the blockchain network and allow anyone to validate it by connecting my signature to my wallet address.
Storing your keys
Storing your keys is the most important decision any digital asset user makes. We discussed in Wallet’s don’t hold your crypto they hold your keys that when you are using an exchange, the exchange is the one holding onto the private key. If you use wallet software, then you are holding them. Holding onto them in the digital sense means that they are stored on your computer or some other storage device. The key is just a long string of letters and numbers and can be stored the same way you would store a word document or other digital information.
Wallet software is downloaded to your computer or phone and runs the crazy math formulas on your device creating a seed phrase, private key, and public key for you. That means that if the company that creates the wallet software gets hacked, your funds are safe. The company never stores your seed phrase or private key information. Instead, it is stored as an encrypted file on your personal device. It also means that if your device gets hacked, you are the only affected. The hacker cannot use your hacked phone to access anyone else's private keys and therefore their digital assets. When you use an exchange, you are relying on the exchange to control, maintain, and secure that private key for you.
Blockchains and Self Sovereignty
The storage of your keys is one characteristic that aligns the blockchain and digital asset industry with the ideology of self sovereignty. As long as you have your private key with an internet connection, you can sign transactions and therefore move digital assets. A single USB could hold the private key that has access to $1B worth of funds. Compare that to the slow transaction time, limitations, and general hoop-jumping that needs to be done to send any amount of money in the traditional financial system. Blockchains give Individuals a technology that provides them monetary self-sovereignty in a way that has never been done before.
With great power comes great responsibility. Using a wallet, means that you are taking full responsibility for your digital assets. For some, the concept of complete responsibility is scary. Storing your private key on your computer is exactly like keeping all your cash in your home. If you light a fire in your kitchen and your house burns down, no one will compensate you for the money that burned up. If your computer gets hacked or you lose your private key, there is no customer support to call. In fact, there are countless stories of people early into crypto throwing away computers with their private keys on them and losing access to millions of dollars.
Despite the risk concerns associated with holding your own keys, many people choose to. The independence and freedom is alluring. Next week we will discuss the different kinds of wallets that exist and what makes each one unique.
Huge shout out to my collaborators from Foster: David Burt
Follow me on Twitter @thatsauchward